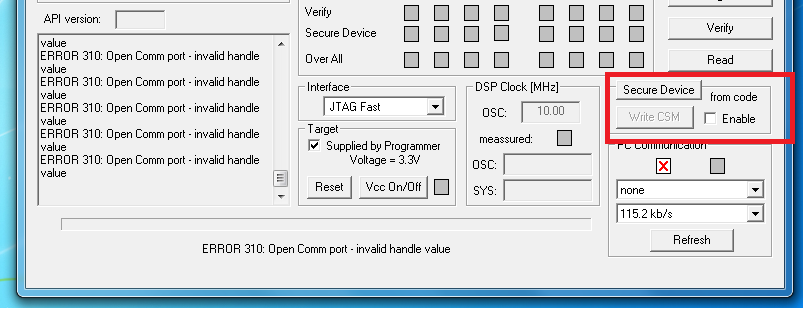
I have completed my development, and would like to engage the CSM to lock my processor. But I am not able to make it work. I can still access my processor through JTAG without unlocking.
I have engaged the CSM by writing the password as recommended by TI ( I think). Attached is my linker command file and assembly file that maps the CSM password and reserved sections. I include these in my build and in the output hex file, i can see the password. so i know its getting written.
Someone please help!
Linker Command File...
/*
NOTES: 1) Stack must be in low 64k data space. See p. 7-5 of Compiler
2) If you move the Stack, adjust main.c, and boot.c
3) This linker command file is only for Large Memory Model code (-ml)
4) If you adjust MAIN_C, adjust chksum in b.bat
5) Unified memory, don't have overlayed sections, except f. loader
since it executes only after the main application has stopped.
*/
--diag_suppress=16002
-l Flash28334_API_V210.lib
-l Flash28335_API_V210.lib
-l rts2800_fpu32.lib
MEMORY
{
/* program memory */
PAGE 0 :
HEADER_C : origin = 0x338000, length = 0x000010 /* appl header */
MAIN_C : origin = 0x338010, length = 0x007F50 /* appl execution space */
BOOT_DATA : origin = 0x33FF60, length = 0x000020 /* Boot Data: Assembly Info */
BOOT_ENTRY : origin = 0x33FFF6, length = 0x000002 /* CPU reset vector */
CSM_RSVD : origin = 0x33FF80, length = 0x000076 /* CSM reserved */
CSM_PSWD : origin = 0x33FFF8, length = 0x000008 /* CSM password area */
/* data memory */
PAGE 1 :
RAM_MODE : origin = 0x000050, length = 0x000008 /* RAM Bootloader Handle */
PIEVECT : origin = 0x000D00, length = 0x000100 /* application vect tbl */
RAMF_R : origin = 0x008000, length = 0x000600 /* ramf ram space */
MAIN_R : origin = 0x008600, length = 0x001600 /* appl ram space*/
STACK_R : origin = 0x009E00, length = 0x000200 /* stack space */
}
SECTIONS
{
.reset:
{
reset.obj(.text)
} > BOOT_ENTRY PAGE = 0
._stack:
{
_stack_start = .;
} > STACK_R PAGE = 1
.ramf: LOAD = MAIN_C PAGE = 0, RUN = RAMF_R PAGE = 1
{
Flash28335_API_V210.lib(.econst)
Flash28335_API_V210.lib(.text)
} LOAD_START(_ramf_l), LOAD_SIZE(_ramf_s), RUN_START(_ramf_r)
.cinit:
{
_cinit_start = .;
*(.cinit)
_cinit_end = .;
} > MAIN_C PAGE = 0
.econst:
{
_econst_start = .;
*(.econst)
_econst_end = .;
} > MAIN_C PAGE = 0
.text:
{
_text_start = .;
*(.text)
_text_end = .;
} > MAIN_C PAGE = 0
.ebss:
{
_ebss_start = .;
*(.ebss)
_ebss_end = .;
} > MAIN_R PAGE = 1
_boot_assm_data :
{
} > BOOT_DATA PAGE = 0
_csm_pswd :
{
} > CSM_PSWD, PAGE = 0
_csm_rsvd :
{
} > CSM_RSVD, PAGE = 0
}
csm.asm File
; Section - csmpasswds
; -This locates the CSM password in the the required section of TI memory.
;
.sect "_csm_pswd"
.int 0x795A ;PWL0 (LSW of 128-bit password)
.int 0x93A0 ;PWL1
.int 0x50A4 ;PWL2
.int 0x2B11 ;PWL3
.int 0xC902 ;PWL4
.int 0xE911 ;PWL5
.int 0xB44D ;PWL6
.int 0x9CB5 ;PWL7 (MSW of 128-bit password)
;----------------------------------------------------------------------
; For code security operation, all addresses between 0x33FF80 and
; 0X33fff5 cannot be used as program code or data. These locations
; must be programmed to 0x0000 when the code security password locations
; (PWL) are programmed. If security is not a concern, then these addresses
; can be used for code or data.
; The section "csm_rsvd" can be used to program these locations to 0x0000.
.sect "_csm_rsvd"
.loop (33FFF5h - 33FF80h + 1)
.int 0x0000
.endloop