We use the MSP430F133 device in a control handle for our machines. A few years ago, we had several instances of these handles becoming non-functional. Upon analysis, I found that the MSP430F133 controllers in them were completely blank, as if a Mass Erase operation had been performed. At the time, after looking into the issue and with help from TI, surmised that noise was possibly getting into the JTAG connection, and initiating an operation with a bad code-protection password. This causes the BSL to do a Mass-Erase. So, I installed an RC filter on the TCK pin, and the problems went away. The newer datasheets recommend a similar filter on the TDI pin as well, which I had not implemented.
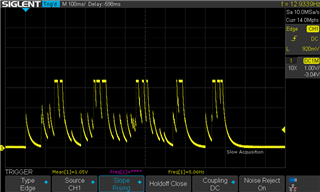
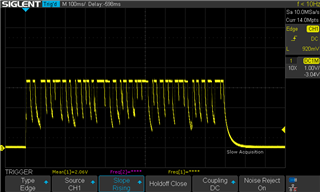
Now, we have a new rash of failures, with the chips coming back completely blank. I believe that this may be due to Vcc instability, as we had a beta setup in a batch of these machines that could cause severe VCC oscillations that this chip would have to endure. However, it's worth noting that there is NO FLASH writing that goes on in our firmware, and from what I gather in these forums is that FLASH erasure or corruption is impossible due to merely having an unstable Vcc. But the vast majority of these units failed overnight.
In my reading of the 'F133 datasheet, this part has no brownout protection, nor a SVS module. The BSL is a lower version than the 2.x that has the ability to disable the "Mass-Erase-on-Bad-Password" functionality.
My question is, has anyone experienced a similar situation with unwanted Mass Erase operations in these chips? And what would be the best course of implementing a solid and decisive solution to prevent this?