Part Number: TMS320F28388D
Other Parts Discussed in Thread: UNIFLASH, SYSCONFIG
Operation
(1) The program can run normally without using DCSM;
(2) After using the Z1 of DCSM to encrypt all the RAM and FLASH that can be encrypted, the program cannot run normally;
(3) If DCSM_unlockZone1CSM is called at the beginning of the main function to decrypt, the program can run normally;
Question 1: Although using the above method (3) can make the program run normally, but does it pose a risk to code security?
① In this case (DCSM_unlockZone1CSM is called at the beginning of main function to decrypt), the code read back by UniFlash using JTAG is still all zero, unless UniFlash also enters CSMPSWD to unlock the chip;
② Using CCS in this case (DCSM_unlockZone1CSM is called at the beginning of main function to decrypt), it is not possible to burn new programs without configuring passwords;
Does the test ①② indicate that the code is already secure? Are there other ways to read back the user's code under these conditions that pose a threat to code security?
Question 2: The cause of the above (2) is located as calling the code of the security zone in the non-security zone;
As shown in the figure below, GSRAM cannot be encrypted. When memcpy needs to be used to move part of the security FLASH code to GSRAM, if there is a need to call other code that is still in the FLASH security area and has not been moved to GSRAM code, It will cause an error that calls the code of the security zone in the non-security zone, so that the program cannot run normally. The best solution, of course, is to replace the GSRAM that carries the code to the destination with LSRAM that can be encrypted, but if the amount of code that needs to be carried to RAM is large, LSRAM alone cannot be loaded, how to solve the problem? In order to avoid calling the code of the secure area in the non-secure area, can only use LSRAM as the transport destination, and the storage of larger GSRAM can only store variables and other data, can not be used as the code running space?
memory map

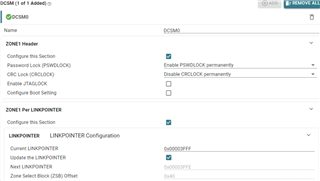
sysconfig DCSM


CMD





