Part Number: MSPM0G1519
Other Parts Discussed in Thread: SYSCONFIG, MSPM0G3507, MSPM0G3519
Tool/software:
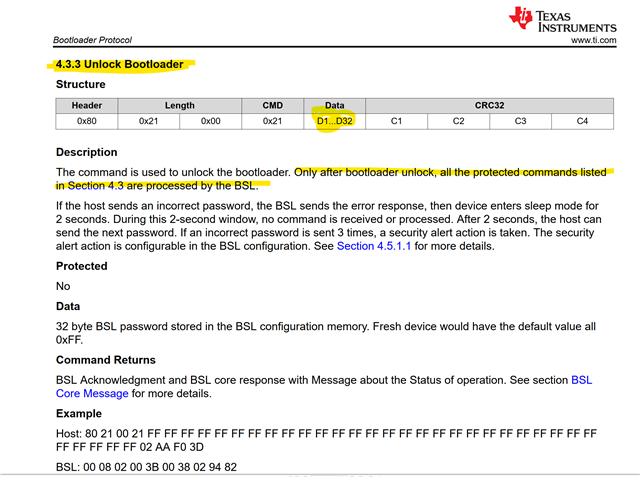
Regarding the BSL password for unlocking most BSL commands for MSPM0G the
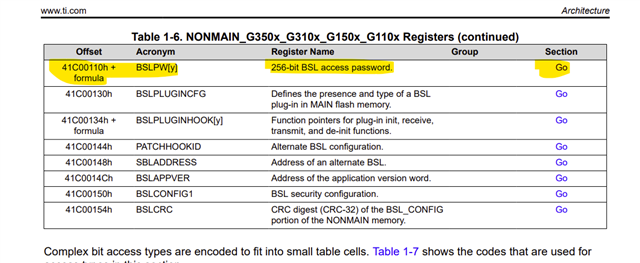
- Technical Reference Manual
- AN: MSPM0 Bootloader Implementation
- MSPM0 Bootloader User Guide
- MSPM0G1519 Datasheet
all mention a 256bit password that need to be presented to unlock those BSL commands.
From this I figured that there will be a plain
presented pwd (256bit) == configured value in BSLPW[y] register (in NONMAIN)
check only.
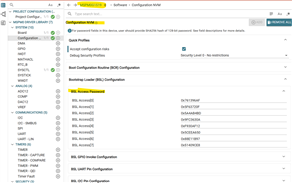
Yet when looking at the description in TI IDE below

I get the impression that there is a hash calculation involved. Meaning
sha256(presented pwd 128bit) == configured value in BSLPW[y] register (in NONMAIN)
Can you please explain which BSL PWD comparison scheme is really used?