Part Number: AM2432
Tool/software:
How to enable secure boot in AM2432
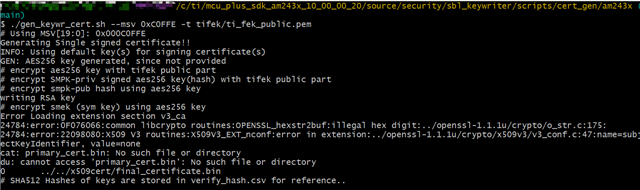
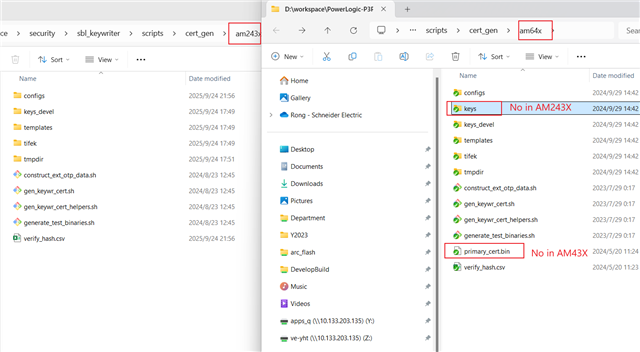
SDK: mcu_plus_sdk_am243x_09_02_00_51
CCS: 12.7.0.00007
chip: am2432ALV
I have accessed secure resource of AM243X, that is mcu_plus_sdk_am243x_09_02_00_51.
But there is no guide for it, the attached ReadMe.txt is a general description and has nothing to do with secure boot.
Please help me for AM2432 Secure Boot configure and test.
Thank you.
BRs
Ronny