Part Number: AM623
Tool/software:
Hello,
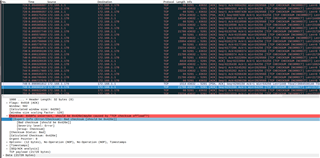
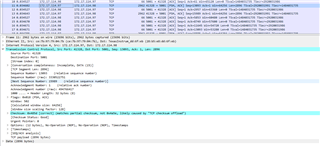
on our AM6234 SoC it looks like TX checksum offloading to CPSW is not supported, like it is stated in errata i2027 but only for AM65x.
Can you confirm that this is the case, or what is wrong with our driver?
I use the Kernel sources from ti-rt-linux-6.1.y branch. In Wireshark I can see that the checksum is untouched and still the partial checksum is transmitted.
After disabling TX checksumming (ethtool --offload eth2 tx off), I do not have any issues.
Thanks