Dear Champs,
I am asking this for our customer.
The user is testing DCSM with their own bootloader.
1.
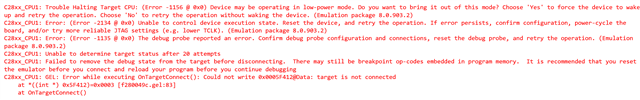
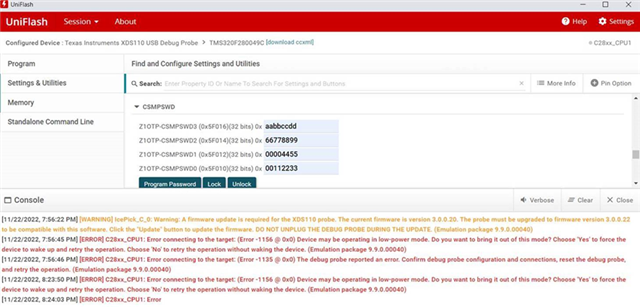
They found there was something wrong like below fig. when they tested DCSM with their bootloader and they could not take F280049 out of this state or unlock it with the password even if they powered cycle the device.
Do you have any idea why and how they can take F280049 out of this state?
2. In their testing,
If they do not use DCSM and only use their app code and bootloader, everything works.
If they use DCSM and only use their app code without the bootloader, everything works.
If they use DCSM with their bootloader, then it fails and become question 1 above after power-cycle.
Their DCSM is running on secure LSx RAM responsible for bank0 flash erase/program but some of bootloader data .cio/.stack/.ebss are in unsecure GSx RAM. Does it matter?
They only use CSM Zone 1 for LSx RAM, all bank0, all bank1.
Do you have any suggestion for them to debug for their bootloader?
Wayne Huang